Microsoft Tuesday issued instructions and a one-click tool to small businesses with on-premises Exchange servers to patch the vulnerability first disclosed by the company March 2, and which criminals have been using to spy on victims’ communications as well as gain access to other parts of their networks.
“We realized that there was a need for a simple, easy to use, automated solution that would meet the needs of customers using both current and out-of-support versions of on-premises Exchange Server,” Microsoft said in a post to a company blog attributed to the MSRC (Microsoft Security Research Center) Team.
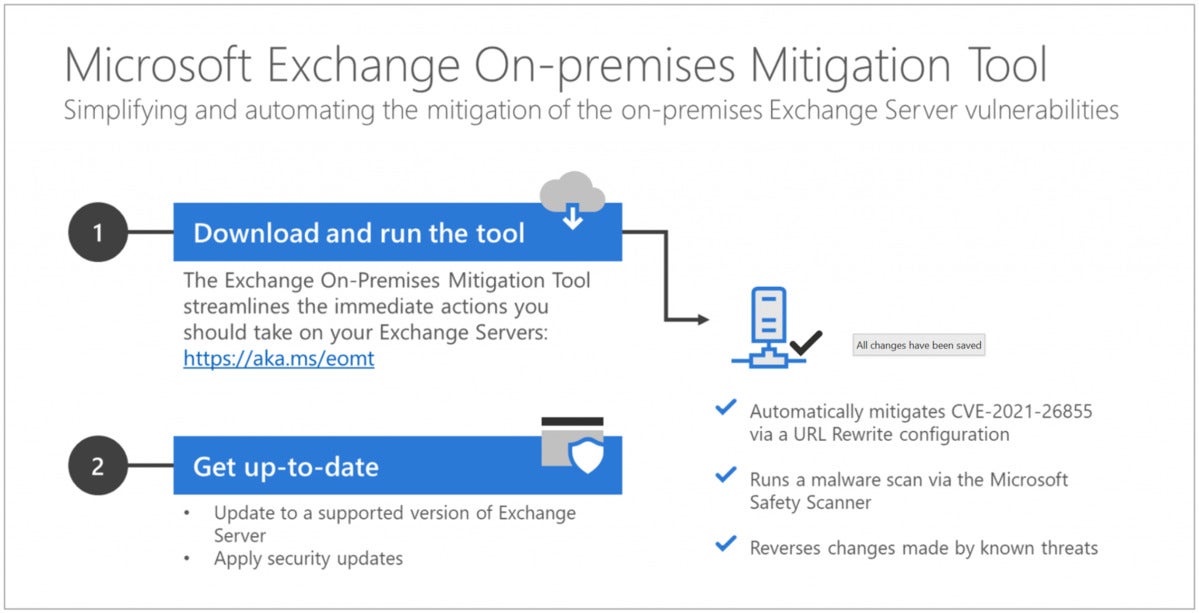
The tool, dubbed (with the usual Microsoft knack of catchy monikers), “Microsoft Exchange On-Premises Mitigation Tool,” is aimed at customers that don’t have dedicated IT personnel or are even “unfamiliar,” Microsoft said, with the patching and update process. The tool works on Exchange 2013, 2016, and 2019, the currently supported editions of the server software. (Exchange 2013 will be supported until April 2023, while the other two editions will be supported until October 2025.)
 Microsoft
MicrosoftMicrosoft’s free tool for small businesses mitigates against attacks on Exchange Server using one of the several vulnerabilities the Redmond, Wash. developer patched March 2. (Click image to enlarge it.)
According to Microsoft, the tool is “not a replacement for the Exchange security update,” but a stopgap measure to defend vulnerable Exchange servers until the customer can deploy the actual fix.
The tool does several things, notably configuring Exchange Server to institute a mitigation for the CVE-2021-26855 vulnerability (one of four now being exploited by cyber criminals). The tool also runs a malware scan using “Microsoft Safety Scan,” a free utility that both sniffs out exploits and attempts to reverse any changes made by attackers. (The scanner, which can also be manually downloaded from here, is live for the following 10 days. Users can trigger it for additional scans at any time after the mitigation through that stretch.)
This was not the first automated script Microsoft has offered customers to mitigate against attacks based on the Exchange Server bugs patched on March 2. Three days after that, Microsoft posted links to multiple mitigation tools, including “ExchangeMitigations.ps1,” a PowerShell script that tackled several of the patched vulnerabilities, including CVE-2021-26855, which was also addressed by the newer On-Premises Mitigation Tool.
“We recommend this script over the previous ExchangeMitigations.ps1 script as it [is] tuned based on the latest threat intelligence,” Microsoft said Tuesday. “If you have already started with the other script, it is fine to switch to this one.”
The Exchange Server vulnerabilities were patched March 2 in one of Microsoft’s rare out-of-band updates, meaning the update was released outside the usual second-Tuesday-of-each-month schedule.
Microsoft’s best source of information on the vulnerabilities and the exploits of them can be found in a security blog post on the Exchange Server attacks.
The attacks quickly jumped from those against the largest organizations to a larger pool of victims as the number of bad actors behind them expanded, that unusual in itself.
Additional guidance for those responsible for maintaining the security of Exchange Server software can be found in a March 16 post to the MSRC blog.



